How AI behavioral analytics is used in cybersecurity
Understand how AI behavioral analytics detects cyber threats by analyzing user and system behavior, reducing risks, false alerts, and improving security.

AI behavioral analytics is the use of artificial intelligence to monitor, analyze, and identify patterns in user and system behavior to detect anomalies and potential security threats.
Rather than depending on static rules, it builds a baseline of normal activity. This includes login patterns, data access behavior, network usage, and system interactions. Once this baseline is established, any deviation is flagged for further analysis.
This approach shifts cybersecurity from “what is known” to “what looks unusual.” It allows organizations to identify threats that would otherwise go unnoticed, especially insider risks and advanced attacks.
Why AI Behavioral Analytics is Critical for Cybersecurity
As cyber threats become more advanced, detection methods need to evolve. AI behavioral analytics addresses gaps that traditional systems cannot handle.
Detecting Advanced Threats:
Modern attacks often mimic legitimate behavior to avoid detection. Behavioral analytics identifies subtle deviations that indicate malicious intent, even when the activity appears normal.
Reducing False Positives:
Security teams often deal with alert fatigue due to excessive false alarms. AI filters noise by focusing on meaningful behavioral changes, allowing teams to prioritize real threats.
Proactive Threat Detection:
Instead of waiting for an attack to trigger alerts, AI behavioral analytics identifies early warning signs. This enables faster response and reduces potential damage.
Adaptive Learning:
The system continuously learns from new data and evolving behaviors. This ensures detection models stay relevant even as attack patterns change.
Continuous Improvement:
With every interaction, the system refines its understanding of normal behavior. This improves accuracy and strengthens the overall security posture over time.
Organizations investing in AI in threat detection are moving towards systems that can predict and prevent attacks rather than just respond to them.
How Behavioral Analytics Works
To understand its impact, it helps to break down how behavioral analytics functions in a real environment.
-
Data Collection: The system gathers data from multiple sources such as user activity logs, network traffic, and application usage. This provides a comprehensive view of behavior across the organization.
-
Behavior Profiling: AI models analyze the data to establish a baseline of normal behavior for users, devices, and systems. This baseline acts as a reference point for identifying anomalies.
-
Anomaly Detection: When behavior deviates from the baseline, the system flags it as suspicious. These deviations may indicate potential threats such as unauthorized access or data exfiltration.
-
Risk Scoring: Each anomaly is assigned a risk score based on severity and context. This helps security teams focus on high-priority threats.
-
Response and Action: The system can trigger alerts, automate responses, or escalate incidents for further investigation. This ensures faster and more effective threat management.
This structured approach allows organizations to detect threats in real time while improving response efficiency.
Types of Behavioral Analytics
Behavioral analytics in cybersecurity can be applied at different levels, depending on what needs to be monitored and protected.
User Behavior Analytics (UBA): Focuses on monitoring user activities such as login patterns, access behavior, and data usage to detect insider threats. UBA also identifies compromised accounts by tracking unusual actions, such as sudden access to sensitive files or abnormal working hours, helping prevent data breaches.
Entity Behavior Analytics (EBA): Extends analysis beyond users to include devices, applications, and systems. This provides a broader view of organizational behavior.EBA can detect misconfigured devices or unauthorized system interactions, reducing the risk of operational failures and malware propagation.
Network Behavior Analytics (NBA): Monitors network traffic to identify unusual patterns that may indicate cyberattacks or unauthorized access. NBA also flags anomalies such as unusual bandwidth spikes or unexpected connections, helping security teams respond to potential DDoS attacks or lateral movement by attackers.
Application Behavior Analytics: Tracks how applications are used and identifies anomalies that could signal vulnerabilities or misuse. Application analytics can also detect unusual API calls or access patterns, helping to prevent exploitation of software vulnerabilities and ensuring regulatory compliance.
Difference Between UEBA, NBA, and ITBA
Understanding these terms helps clarify how behavioral analytics is applied across cybersecurity systems.
|
Type |
Focus Area |
Key Functions |
Additional Insights |
Example Use Cases |
|
UEBA (User and Entity Behavior Analytics) |
Users and systems |
Monitors user activities, access patterns, and entity behavior to detect anomalies |
Provides a holistic view of organizational behavior, combining user actions with system interactions for better threat detection |
Detecting compromised accounts, insider threats, unusual file access, or abnormal logins |
|
NBA (Network Behavior Analytics) |
Network traffic |
Analyzes traffic patterns, bandwidth usage, and data flow anomalies |
Detects malicious network activity, unusual connections, and potential lateral movement by attackers |
Identifying DDoS attacks, suspicious data transfers, and unauthorized network access |
|
ITBA (IT Behavior Analytics) |
ITBA (IT Behavior Analytics) |
Monitors servers, endpoints, and system-level activities for irregular behavior |
Helps prevent system misconfigurations, security breaches, and operational failures |
Helps prevent system misconfigurations, security breaches, and operational failures |
While each serves a specific purpose, combining them yields a stronger, more layered defense.
Applications of AI Behavioral Analytics in Cybersecurity
AI behavioral analytics is used across multiple areas to strengthen security operations.
-
Insider Threat Detection: Identifies unusual user behavior that may indicate malicious intent or compromised accounts.
-
Fraud Detection: Detects abnormal transaction patterns and suspicious financial activities.
-
Account Compromise Detection: Flags login attempts and access patterns that deviate from normal behavior.
-
Data Loss Prevention: Monitors data access and transfer activities to prevent unauthorized sharing or leaks.
-
Threat Hunting: Enables security teams to proactively search for hidden threats within the system.
Organizations looking to improve SOC with AI security analytics are using these applications to enhance visibility and response capabilities.
Key Advantages of Behavioral Analytics
The adoption of behavioral analytics brings measurable benefits to cybersecurity operations.
-
Improved Threat Detection: Identifies both known and unknown threats by focusing on behavior rather than signatures. It helps security teams uncover sophisticated attacks that traditional systems might miss.
-
Reduced False Alerts: Filters out noise and highlights meaningful anomalies, improving efficiency for security teams. Analysts can focus on real threats without being overwhelmed by unnecessary alerts.
-
Faster Response Time: Enables quicker identification and mitigation of threats, reducing potential damage. This rapid reaction helps minimize the impact on business operations and data integrity.
-
Scalability: Handles large volumes of data and interactions without compromising performance. It allows organizations to maintain security across growing networks and evolving infrastructures.
-
Better Decision Making: Provides actionable insights that support predictive analytics in decision making, helping organizations stay ahead of threats. Security leaders can prioritize resources and strategies more effectively based on data-driven intelligence.
These advantages make behavioral analytics a critical component of modern cybersecurity strategies.
Best Practices for Implementing Behavioral Analytics Solutions
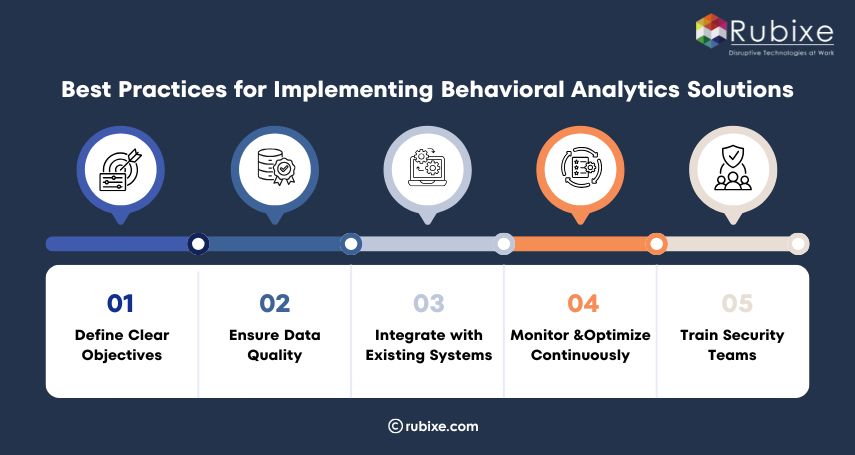
Successful implementation requires a structured approach and alignment with organizational security goals. Proper planning ensures that behavioral analytics delivers maximum value while minimizing risks.
-
Define Clear Objectives: Identify what you want to achieve, whether it is threat detection, fraud prevention, or regulatory compliance. Clearly defined objectives help prioritize use cases and ensure that analytics models focus on the most critical security challenges.
-
Ensure Data Quality: High-quality, consistent, and clean data is essential for accurate analysis and reliable results. Inaccurate or incomplete data can lead to false positives or missed threats, reducing the effectiveness of AI anomaly threat detection.
-
Integrate with Existing Systems: Behavioral analytics should work seamlessly with current security tools, SIEM systems, and IT infrastructure. Smooth integration allows organizations to leverage predictive analytics in decision-making and enhances overall SOC efficiency.
-
Monitor and Optimize Continuously: Regular evaluation and refinement of behavioral models help improve accuracy and adapt to emerging threats. Continuous optimization ensures that AI in threat detection evolves alongside the changing tactics of cyber attackers.
-
Train Security Teams: Security teams must understand how to interpret insights and respond effectively to behavioral alerts. Training ensures that human analysts can complement AI-driven insights, making incident response faster and more precise.
Applying ML in cybersecurity allows systems to learn from patterns and detect anomalies proactively. This adaptive learning enhances AI anomaly threat detection and strengthens the organization’s overall cybersecurity posture.
How Rubixe Deploys Behavioral Analytics in Your Cybersecurity Architecture
Implementing behavioral analytics requires both technical expertise and a clear understanding of business operations.
Rubixe approaches this by integrating AI-driven behavioral analytics into existing security frameworks without disrupting workflows. The focus is on building systems that detect anomalies in real time while aligning with operational needs.
-
Customized models are developed based on organizational behavior patterns
-
Integration with the existing security infrastructure ensures seamless deployment
-
Continuous monitoring and optimization improve detection accuracy over time
-
Scalable solutions support growing data and security requirements
As an experienced AI Cybersecurity service provider, Rubixe helps organizations move from reactive security models to proactive threat management systems.
Working with an experienced AI development company ensures that behavioral analytics is implemented effectively, delivering both security and operational value.