What is AI Anomaly Detection Security?
AI anomaly detection security identifies unusual behavior in systems and networks to detect cyber threats using machine learning and AI cybersecurity services.
What if a cyberattack is already happening inside your network, but no one realizes it until the damage is done?
Many businesses assume their firewalls, antivirus tools, and monitoring systems are enough to stop attacks. But modern cyber threats rarely follow predictable patterns. Hackers now operate quietly inside systems, using legitimate credentials and normal-looking activity to avoid detection.
AI anomaly detection security becomes critical in this situation. Instead of looking only for known threats, it focuses on identifying unusual behavior within a system. When integrated into an advanced AI cybersecurity service, anomaly detection helps organizations identify hidden threats before they escalate into serious breaches.
The Growing Challenge of Modern Cyber Threats
Cybersecurity has changed dramatically in the past decade. Traditional security systems were designed to detect known threats using predefined rules and signatures. While this method worked well for earlier types of malware and viruses, modern attacks have evolved.
Today’s cybercriminals use techniques that bypass traditional detection systems. Some of the most common attack strategies include:
-
Zero-day exploits that target unknown vulnerabilities
-
Credential theft that allows attackers to log in as legitimate users
-
Insider threats where employees misuse access privileges
-
Advanced persistent threats (APTs) that quietly operate inside networks for months
These attacks often appear as normal activity. For example, a hacker using stolen login credentials may look like a legitimate employee accessing company systems.
Traditional security tools may fail to detect these situations because the activity does not match any known threat signature.
This is why businesses are increasingly turning to AI-powered cybersecurity solutions that focus on behavior analysis rather than just threat databases.
Understanding AI Anomaly Detection Security
AI anomaly detection security is a cybersecurity approach that uses artificial intelligence and machine learning to identify unusual patterns in system behavior, network activity, or user actions.
Instead of relying solely on predefined rules, the system studies normal operational patterns and learns how users, devices, and networks typically behave.
Once this baseline is established, the AI continuously monitors activity across the environment. Any behavior that deviates from the normal pattern is flagged as a potential threat.
This approach allows organizations to detect security risks that traditional tools might miss.
Some examples of anomalies that AI systems can detect include:
-
A user logging into the network from an unusual geographic location
-
A device attempting to access sensitive data that it has never accessed before
-
A sudden spike in file downloads or data transfers
-
Unexpected communication between internal servers
-
Logins occurring outside normal working hours
Each of these activities could indicate a security risk, even if they initially appear harmless.
How AI Anomaly Detection Works
AI anomaly detection relies on machine learning algorithms that analyze large volumes of security data. The process typically involves several stages.
1. Data Collection
The first step involves collecting data from various sources across the IT environment. This data provides insights into how systems normally operate.
Common data sources include:
-
Network traffic logs
-
User login behavior
-
Application access patterns
-
Endpoint activity
-
Server logs
-
Cloud infrastructure events
The more data the system collects, the more accurate the behavioral analysis becomes.
2. Building a Behavioral Baseline
Machine learning models analyze historical data to identify patterns of normal activity.
For example, the system may learn:
-
When employees typically log in and log out
-
Which applications do users commonly access
-
Typical data transfer volumes
-
Normal communication patterns between servers
This behavioral baseline acts as a reference point for detecting anomalies.
Every system, organization, and user behaves differently, so creating a customized baseline is essential for accurate detection.
3. Continuous Monitoring
Once the baseline is established, the AI system monitors activity in real time. Every login, file transfer, and network connection is compared against the expected behavioral patterns.
If the system detects activity that significantly deviates from the baseline, it marks it as an anomaly.
Unlike static rule-based systems, AI models adapt over time as behavior changes.
4. Alerting and Response
When suspicious activity is detected, the system triggers alerts for the security team.
Depending on the configuration, the AI cybersecurity platform may also take automated actions such as:
-
Blocking suspicious IP addresses
-
Locking compromised accounts
-
Isolating affected systems
-
Initiating further threat analysis
These automated responses significantly reduce the time required to contain security incidents.
Why AI Anomaly Detection is Important for Businesses
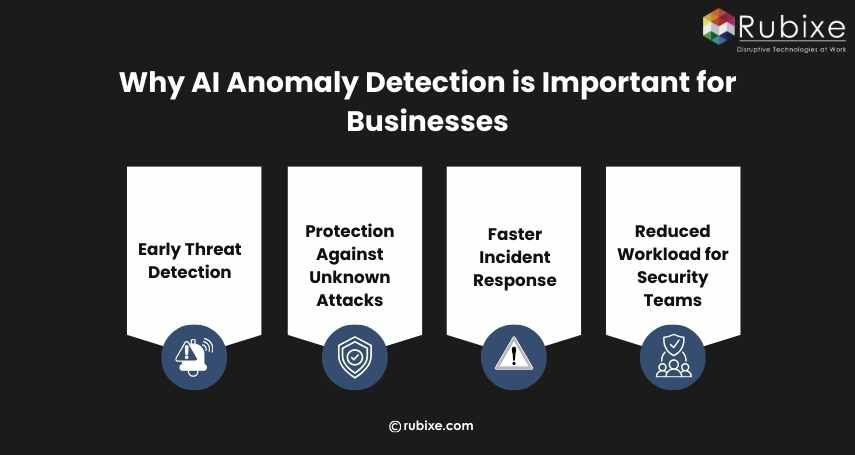 Cybersecurity incidents can cause serious financial and operational damage. Data breaches often lead to regulatory penalties, loss of customer trust, and long-term reputational harm.
Cybersecurity incidents can cause serious financial and operational damage. Data breaches often lead to regulatory penalties, loss of customer trust, and long-term reputational harm.
Implementing AI anomaly detection security offers several key advantages.
1. Early Threat Detection
Many cyberattacks go unnoticed for weeks or even months. During this time, attackers may collect sensitive data or move laterally within the network. AI systems can detect suspicious activity much earlier by identifying unusual behavior patterns.
2. Protection Against Unknown Attacks
Traditional security tools rely heavily on known threat signatures. However, new attack methods are constantly being developed. AI-based security focuses on behavioral analysis, allowing it to detect threats even when the attack pattern is previously unknown.
3. Faster Incident Response
Speed is critical during a cybersecurity incident. The faster a threat is detected and contained, the lower the potential damage. AI-driven systems provide real-time alerts and automated responses, helping organizations react quickly.
4. Reduced Workload for Security Teams
Security teams often deal with thousands of alerts daily, many of which turn out to be false positives.
Machine learning cybersecurity systems improve accuracy over time, helping reduce unnecessary alerts and allowing security professionals to focus on real threats.
Where AI Anomaly Detection is Used
AI-based anomaly detection is used across many areas of cybersecurity.
1. Network Security: AI monitors network traffic to identify unusual data flows, suspicious connections, or abnormal communication between devices. This helps detect malware infections, lateral movement, and unauthorized access attempts.
2. User Behavior Analytics: User behavior analytics focuses on how individuals interact with systems. AI systems detect suspicious activities such as unusual login times, abnormal data access patterns, or excessive file downloads. These behaviors may indicate insider threats or compromised accounts.
3. Cloud Security: Cloud environments generate massive volumes of activity logs. Monitoring these environments manually is nearly impossible. AI anomaly detection systems help identify unusual cloud activity such as unauthorized access or abnormal data transfers.
4. Fraud Detection: Financial institutions use anomaly detection to identify suspicious transactions.
For example, if a credit card is suddenly used in multiple countries within a short time, the system flags it as a potential fraud case.
AI Anomaly Detection vs Traditional Security
|
Feature |
Traditional Security |
AI Anomaly Detection |
|
Detection Method |
Signature-based |
Behavior-based |
|
Unknown Threats |
Difficult to detect |
Can detect |
|
Response Speed |
Manual investigation |
Real-time alerts |
|
Learning Ability |
Static rules |
Self-learning models |
|
Insider Threat Detection |
Limited |
Strong detection |
Example of AI Anomaly Detection in Action
A financial organization implemented an AI based anomaly detection system to monitor employee access patterns. The system noticed a login attempt from an employee account at an unusual time and from a new device.
Within minutes, the system also detected large database access requests that were not part of the employee's normal behavior.
The AI platform flagged the activity as suspicious. After the investigation, the security team discovered the employee’s credentials had been compromised in a phishing attack.
Because the anomaly was detected early, the company prevented a major data breach.
How AI Cybersecurity Services Strengthen Security
Implementing AI security systems requires technical expertise, continuous monitoring, and ongoing optimization.
This is why many businesses rely on a reliable AI cybersecurity service to continuously monitor networks and detect abnormal behavior before cyber threats cause damage.
These services typically offer:
-
AI-powered threat detection systems
-
Continuous network monitoring
-
Behavioral analytics tools
-
Automated incident response
-
Security reporting and analysis
-
Integration with existing security platforms
By combining an AI development company with expert oversight, organizations gain a more robust security strategy.
The Future of AI in Cybersecurity
Cyber threats are becoming more automated and sophisticated every year.
Attackers are already using artificial intelligence to launch more effective phishing campaigns, bypass detection systems, and automate attacks.
To defend against these threats, businesses must adopt equally advanced technologies.
AI-based cybersecurity tools are expected to play an even larger role in areas such as:
-
Predictive threat intelligence
-
Automated security operations
-
Real-time attack prevention
-
Advanced behavioral analytics
Organizations that invest in AI-driven security today will be better prepared to handle future threats.
Attackers increasingly rely on subtle tactics that blend into normal system activity, making them difficult to detect with rule-based security systems.
FAQs
1. What is AI anomaly detection in cybersecurity?
AI anomaly detection identifies unusual behavior in networks, systems, or user activity using machine learning models.
2. How does AI detect cyber threats?
AI analyzes large volumes of data, learns normal behavior patterns, and flags activities that deviate from those patterns.
3. Why do businesses need AI cybersecurity services?
AI cybersecurity services help organizations detect hidden threats, reduce response time, and improve overall network protection.
AI anomaly detection security addresses this challenge by analyzing behavior patterns and identifying unusual activity in real time.
When combined with a reliable AI cybersecurity service, organizations gain stronger protection against unknown threats, faster incident detection, and more efficient security operations.
For businesses operating in today’s digital environment, adopting AI powered cybersecurity is not just a technological upgrade. It is a necessary step toward building a smarter, more proactive defense against modern cyber threats.